Attending FOSDEM 2014 in Brussels
thierrym6 min read

On the 1st & 2nd of February 2014, Brussels became the place where to learn and to train for a plethora of tech-savvy women, men, and robots. It was all about this year’s new edition of FOSDEM, which took place once again at the ULB (Université Libre de Bruxelles) Solbosch Campus for openness’s sake.
Since I really enjoyed spending these two days there, surrounded by thousands of geeks literally, I’ve decided to write this article to encourage the readers to plan the trip with enough time upfront for the upcoming editions (especially as access to all tracks is free as in free beer!).
With over 7k visitors attending half of a thousand tracks, the IPv6 installation was totally worthwhile and held solid until the end. Seriously, when was the last time, you didn’t have irreversible issues with wireless networks when attending some event?
Though I personally had no choice in connecting to the double stack network from time to time, the sole availability of the latter is a perfect reminder of all the care, the volunteers donated all along these two days. The huge success reached on this weekend also proves how institutions and public commonalities can be put to use in developing even more synergy within existing and yet-to-be-built open source project communities.
Security
By pointing me at an article posted on the Tor project blog a few months ago, Nicolas Bazire drew my attention to deterministic builds. One of the many risks incurred by core OSS project contributors would be to have a single compromised machine, becoming susceptible to infecting millions of others in a snowball effect.
Jérémy Bobbio (Debian maintainer) decided to work from there with a clear mission statement asserting that it should be possible to reproduce, byte for byte, every build of every package in Debian.
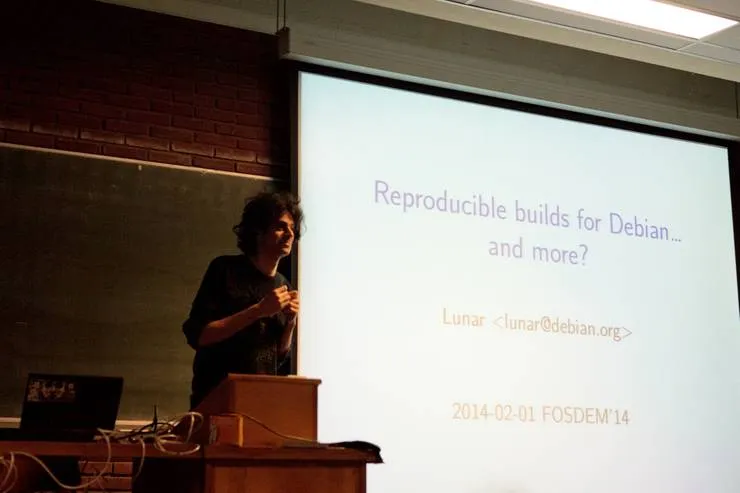
This is what led me to one of the first sessions in the distributions devroom of this Saturday morning, where Jérémy Bobbio a.k.a. Lunar at Debian dot org, explained how this goal could be achieved by
- recording the build environment,
- reproducing the build environment,
- eliminating unneeded variations.
Provided that most of the unneeded variations originate from
- timestamps,
- build path,
- hostname, username, uname,
- files list order.
The beginning of a solution would consist in
- sharing a standard virtual machine,
- installing packages from snapshots.debian.org
- applying plenty of other smart tricks as described on the reference wiki like:
- passing “—enable-deterministic-archives” to binutils,
- timestamps with environment variables,
- patching gzip,
- taking benefit of stable file list in archives.
By the time of the conference, Lunar had achieved a 62% success rate with 3196 packages out of 5151 which can be built in a deterministic way i.e. with same checksums obtained for same binaries.
He insisted on the fact this can only be part of the solution and not a unique solution to improve the overall security of the build toolchain.
Lunar also called for contributors (targeting the PHP registry among many others for Debian) to extend the current coverage, as himself started to work on this project at DebConf2013, which now requires more hands.
Anybody interested in security in general, closely related to Debian and other distributions or willing to contribute, can subscribe to the official Reproducible builds mailing list.
Mozilla Track
In the Mozilla track, Srikar Ananthula described how Mozilla Persona can be a better way to sign-in with no need to store passwords, nor to rely on third-parties.
Mozilla WebMakers is already relying on it and lots of existing libraries and plugins already implement the Browser Id protocol.

Fabien Cazenave shed some lights on The state of Firefox OS.
According to Kazé, the days of “Flash and Retry” experience are over (mostly).
Now that a healthy 12-week release cycle has been established, new web APIs are coming with:
* DataStore API
* Shared workers
A reference device (InFocus 10″, 1280×800x24bit, 16GB Storage, 2GB RAM) has been selected to build FirefoxOS on tablets.
As a result, developers will very soon be able to sign up for participating in the contribution program.
Legal and policy issues
Besides, I had the pleasure to attend my first conference on legal and policy issues with John Sullivan (executive director of the free software foundation) with “JavaScript, If you love it, set it free.”
After recalling some of the biggest recent successes of the foundation (sales of the Gluglug X60 as one of the computers being endorsed to respect our freedom), he proposed a couple of implementations to address the issue of licensing JavaScript code served by websites.
The basic freedom checklist requires
- license notice and possibly a copy of the free license,
- complete source code (i.e. a preferred form of a program for modification).
Privacy

Have you ever been looking to replace your current webmail? Bjarni R. Einarsson has a more than decent solution to offer.
As highlighted in his mailpile introduction, the state of e-mail was kind of stuck in the 90s.
Provided cloudy email is worse for freedom than closed source, mailpile team decided to focus on
- making software, FOSS folks enjoy
- hacking on,
- want to use ;
- making e-mail encryption understandable,
- make decentralization easy,
- find better business models for e-mail.
A very neat web interface has been crafted by MailPile team.
Mailpile alpha version has been released with PGP encryption and signatures and search engines.
Moreover, developers can already play around with a REST API and a command-line interface. Multiple mailbox formats are supported. Spam filters learn from manually tagged emails, messages the user reads, replies to or forwards.
Graph databases
In the morning of the following day, Armando Miraglia (known as a commiter of sshguards) demonstrated the new Giraph APIs for Python, Rexster and Gora. Giraph is used for large scale processing with Hadoop and it is an open-source implementation of Pregel. Armando’s fork supports writing user logic in languages other than Java such as Python.
Davy Suvee illustrated The power of graphs to analyze biological data with an exploration platform (BRAIN).
This platform comes as a stack built to relate 23 million biomedical articles and it can be separated into three distinct layers with:
- meta-data stored with MongoDB,
- graphs persisted into Neo4J
- end-user interface built with Swing
JavaScript
Entering the JavaScript devroom was not trivial but I eventually managed to get a seat there. From what I have heard, it was the first time, JavaScript has its fully dedicated room at FOSDEM appart from the Mozilla tracks.
Robert Kowalski mentioned useful subcommands to execute with npm like config, repo, outdated.
In his talk entitled “Hidden gems in npm”, he revealed npmd in particular, as it provides:
- offline search,
- offline publishing with queuing,
- full caching of installed modules.
Afterward, Laurent Eschenauer showcased how to pilot AR. Drone in JavaScript.
The main principles behind the drones flight automation were exposed:
- Remote control API,
- State estimation (or figuring where a drone is),
- Motion control with PID,
- Path planning.
Testing and automation
Last but not least, Sebastian Bergmann was a speaker at FOSDEM for the first time in the testing and automation developer room.
He told us the story of “Pride and Prejudice: Testing the PHP World” or introduced how he gave birth to PHPUnit application out of pain - by delegating the latter to machines using automation.

Hopefully, we will have the opportunity to attend the next series of the conference at FOSDEM 2015 and we might even meet with some of you there in a crowded dev room.